" Trust is paramount when building your first line of defense "
Frontline’s security solutions are a way of doing business that is more than a portfolio of services and products. It’s about creating a holistic plan that can be implemented Day 1 with your cyber team! This is accomplished by bringing 100+ years of combined security and cyber expertise together to engineer the best solutions. The knowledge of each individual expert on the FrontLine team is equally important because a team with a vast array of experience creates a pragmatic strategy for your particular needs.
Let FrontLine build your first line of defense through:
All of this leads to bottom-line performance with fewer risks.
Scalable solutions from small business to large enterprise
Targeted and impactful outcomes
Respect of budget constraints
Leading edge technologies and know how
Ensuring maximum return on investment

Incident Response
Managed Security Monitoring 24/7/365
Secure Coding
Secure Data Management
Security Services

Software

Infrastructure
Solution Planning
Professional Services
Risk Assessments
A risk assessment is about understanding, managing and controlling the cyber risk and security problems across the entire Organization. We conduct thorough reviews to include policies, procedures, training, network, physical security, etc.
Vulnerability Assessments
Examining the security posture on an organization to discover and remediate vulnerabilities in the network, then delivering the results and remedies in a detailed report
Penetration Testing
etration Testing Breaking through the shell to find weaknesses on the network from the inside out and outside with a full range of pen testing services available to fulfill compliance regulatory requirements

External Pen Test

Internal Pen Test
Network Security Testing & Evaluation
Evaluating the network architecture and security policies in each business/operational unit to find weaknesses that could take limit operations or bring down entire systems
Compliance Assessments
s Measuring your network against industry and government standards to maintain compliance.(i.e. NIST, HIPPA, GDPR, PCI Prep, Financial, etc.)
Incident Response and Forensics
Helping organizations respond, investigate and recover from ransomware and other cyber attacks
Secure App Development and Testing
Developing applications with a positive security posture from the beginning to protect the user and provider from data breeches
Managed Security Services
An innovative capability that offers a full range of information security services to protect networks and data.

24 X 7 X 365 person in the chair security monitoring of IT, OT/ICS, IoT networks

Incident response and investigations, including containment, analysis, and restoration of operations

Digital forensics investigative services

Threat assessment report of risks to programs, technologies, or systems, based on open and intelligence sources

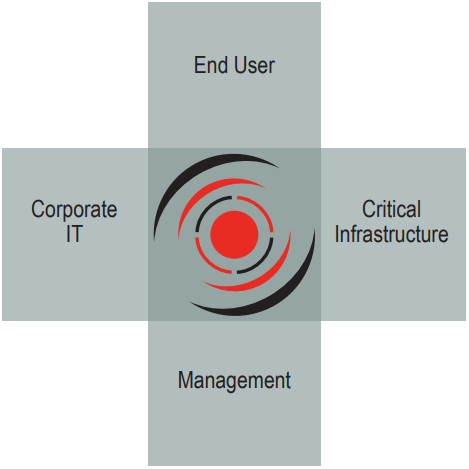
FrontLine connects and protects your entire organization. From the end user all the way to your executive leaders.
FrontLine Staff Certifications:
 GCIH
GCIH CEH
CEH CISSP
CISSP Certified Pen Testers
Certified Pen Testers Certified hacking forensics investigators
Certified hacking forensics investigators Certified OT/SCADA architects
Certified OT/SCADA architects
Professional Experience of FrontLine Staff:
 OT/ICS Red Team leads
OT/ICS Red Team leads Air Force Critical Infrastructure Security Project Manager
Air Force Critical Infrastructure Security Project Manager DoE laboratory OT/ICS engineers
DoE laboratory OT/ICS engineers Former USAF Cyber Warfare Officer
Former USAF Cyber Warfare Officer
